Keeping the gate locked on your IoT devices: Vulnerabilities found on Amazon's Alexa - Check Point Research

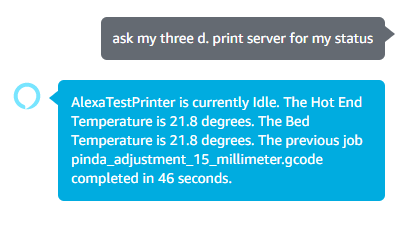
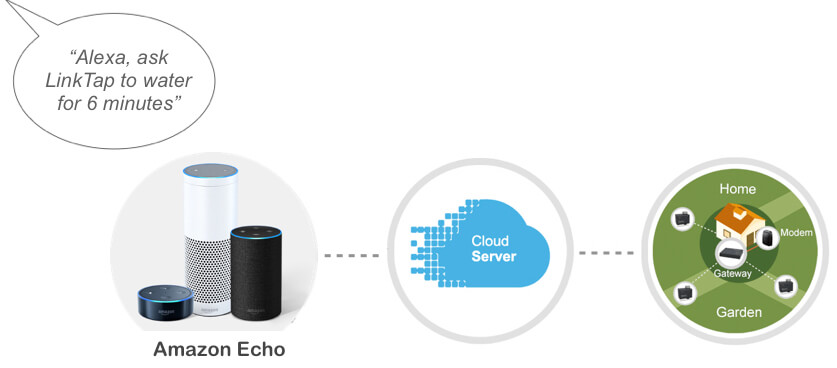
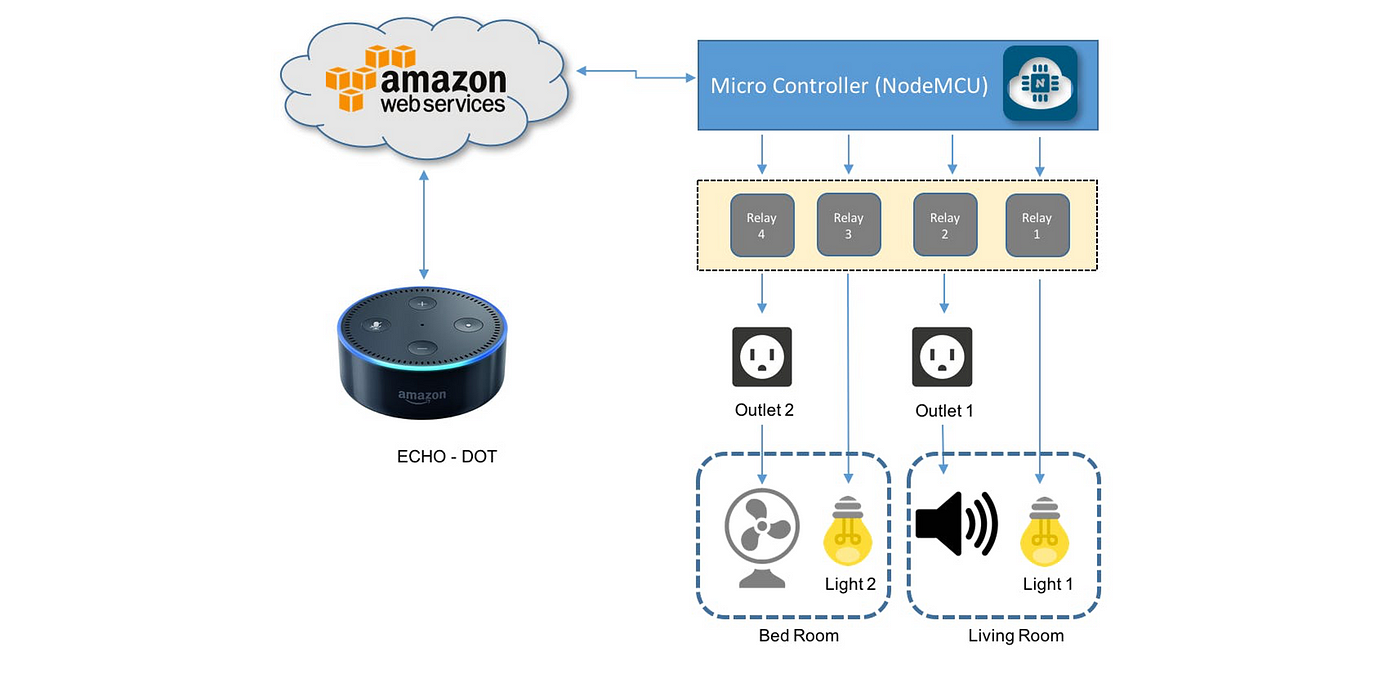
Develop Alexa Custom Skill with AWS Lambda to Control IoT Device | by Priyal Walpita | Coinmonks | Medium
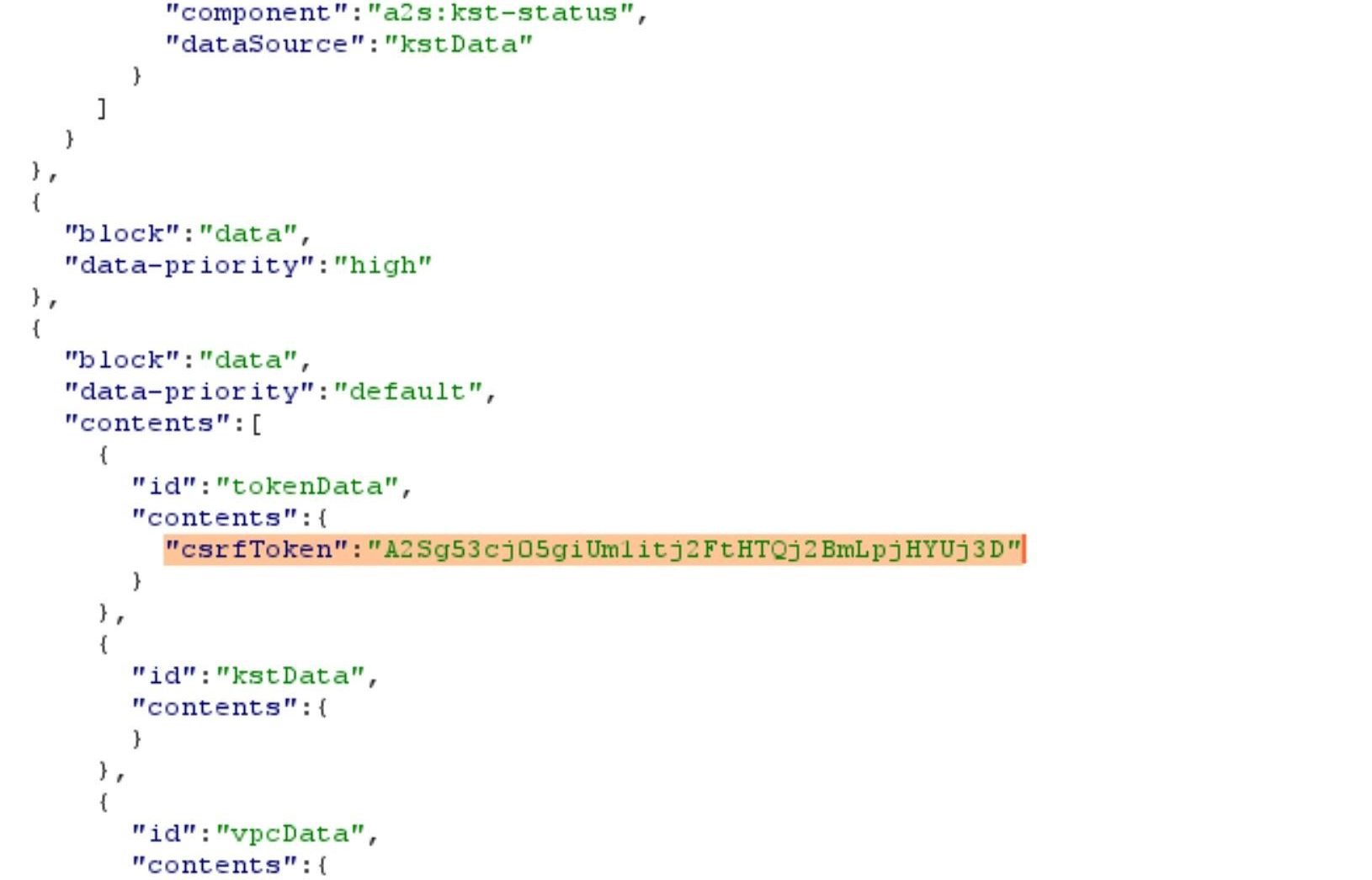
Keeping the gate locked on your IoT devices: Vulnerabilities found on Amazon's Alexa - Check Point Research
:max_bytes(150000):strip_icc()/001_connect-echo-dot-to-wifi-5198657-026e7a6b63eb409a88288e6fc621d0a5.jpg)



:max_bytes(150000):strip_icc()/twitter_alexa_ss-5c6599bf46e0fb0001a91e2f.png)